VTP automates VLAN propagation across switches—but a single switch with a high revision number can wipe all VLANs from your network. Learn how to configure VTPv3, manage revision numbers, and avoid the most dangerous VLAN mistake.
VLAN Trunking Protocol (VTP) promised a seductive simplification: create a VLAN on one switch and it propagates automatically to all others in the domain. Today, VTP is almost universally disabled or relegated to transparent mode because the revision number mechanism can destroy your VLAN database in seconds. Understanding VTP's dangerous defaults and how to configure VTPv3 safely is essential for anyone managing multi-switch environments.
What VTP Does
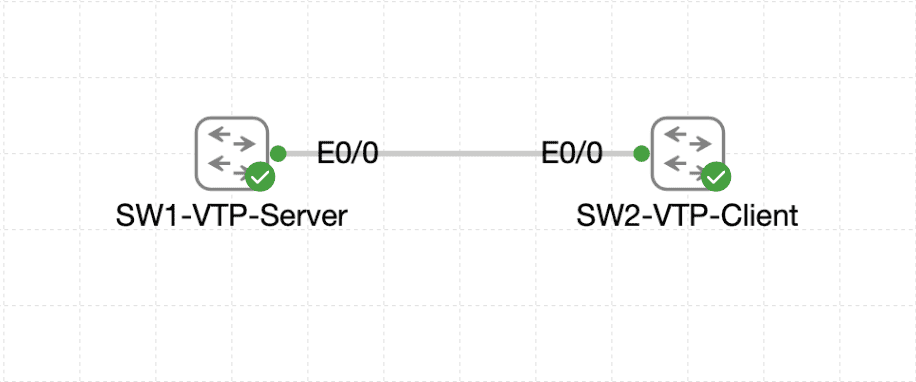
VTP synchronizes VLAN databases across switches by flooding VLAN advertisements through trunk ports. Instead of manually creating VLANs on every switch, you create them once on a VTP server and servers/clients receive the updates.
Without VTP: - Create VLAN 10 on CORE-SW1 → only CORE-SW1 knows about it - Create VLAN 10 on DIST-SW1 → two switches have VLAN 10 - Create VLAN 10 on all three access switches → repeat three times
With VTP enabled: - Create VLAN 10 on CORE-SW1 (configured as server) → VLAN 10 propagates to DIST-SW1, DIST-SW2, and all access switches automatically
However, this synchronization is driven by a revision number. When you add a VLAN, the server increments its revision number and broadcasts "I have VLAN 10 at revision 5." Every other switch receives this and says "I need to update to revision 5." If another switch has revision 6 (perhaps it was a VTP server in a different lab), it floods revision 6, and all other switches erase their VLAN database to match revision 6—wiping VLANs 10-50 in the process.
VTP Domains
VTP operates within a domain, a named boundary that prevents switches in different domains from sharing VLAN information. A switch in domain "PRODUCTION" ignores VTP updates from a switch in domain "LAB".
Catalyst 9000 switches default to a blank domain name, meaning VTP is effectively disabled (no domain = no updates). You must explicitly set the domain name for VTP to activate:
CORE-SW1(config)# vtp domain PRODUCTION
Now CORE-SW1 listens for and sends VTP updates for domain "PRODUCTION" only. Any switch without domain "PRODUCTION" configured won't participate.
VTP Modes
Every switch operates in one of four VTP modes:
Server Mode - Can create, modify, and delete VLANs - Increments revision number when VLANs change - Floods updated VLAN database to all clients and other servers - Receives VLAN updates from other servers (highest revision wins) - Stores VLAN database in NVRAM (survives reboot) - Default mode on most Catalyst switches
Client Mode - Cannot create, modify, or delete VLANs locally - Receives VLAN updates from servers - Forwards updates to other switches (acts as a relay) - Stores VLAN database in RAM (lost on reboot, unless device is Catalyst 9000 which saves to NVRAM in VTPv3) - Useful for read-only VLAN database consistency - Dangerous because any misconfigured VLAN on the server propagates automatically
Transparent Mode - Does not participate in VLAN synchronization - Can create, modify, and delete VLANs locally (they don't propagate) - Forwards VTP updates but doesn't process them (acts as a relay for other switches) - Useful for lab switches or test environments - Default on Catalyst 2960 and older platforms; requires explicit configuration on 9000 series
Off Mode (VTPv2 and VTPv3 only) - VTP is completely disabled - No VLAN synchronization, no forwarding of VTP updates - Useful for switches that should be isolated from the domain - Cleaner than transparent mode for "never participate" designs
VTP Version Differences
VTPv1 (Legacy)
VTP v1 was the original implementation: - Only VLAN IDs 1-1005 supported (extended VLANs 1006-4094 ignored) - Every server must have matching revision numbers to sync (no hierarchy) - No authentication - No extended VLAN support - No off mode (only server, client, transparent)
VTPv2 (Improved but Still Dangerous)
VTPv2 added: - Token ring VLAN support (rarely used) - Consistency checking (warns if VLAN config is inconsistent) - v1 transparency mode (compatible with v1 switches) - Authentication via password (plaintext, not cryptographic) - Off mode (disable VTP completely) - Still limited to VLAN IDs 1-1005
VTPv3 (Current Best Practice)
VTPv3 is substantially safer and is the only version recommended for new deployments: - Extended VLAN support (1-4094) - Primary and secondary servers (only primary increments revision) - Authentication via SHA-1 (or MD5 in hybrid mode) - Hidden password (not plaintext) - Off mode - Per-VLAN STP (PVST) support built-in - Catalyst 9000 defaults to VTPv3
VTPv3 introduces a primary server and secondary servers: - Only the primary server increments the revision number when VLANs change - Secondary servers receive updates but don't modify the revision - To change a secondary to primary, you use vtp primary command - This prevents catastrophic revision number collisions
Revision Number Disaster Scenario
This is the most dangerous VLAN mistake, and it happens faster than you think:
Day 1 Setup (Lab Network) - CORE-SW1 is configured as VTP server in domain "PRODUCTION" - You create VLANs 10, 20, 30 and promote to revision 3 - Network runs fine for weeks
Day 50 Disaster - A tech brings in an old Catalyst 9300 from another lab - That switch was VTP server in domain "PRODUCTION" from a previous project - It has revision 15 in its NVRAM from months of VLAN modifications in the old lab - They connect it to a trunk port, hoping to "refresh it" in the production domain - VTP advertisement arrives: "I am revision 15 in domain PRODUCTION" - All other switches receive this and think: "We're at revision 3, but this switch has 15! Our VLAN database is obsolete!" - All switches erase their VLAN database and replace it with the new switch's database - New switch has no VLANs (or only old test VLANs) - Production VLANs 10, 20, 30 vanish from the network - All ports revert to VLAN 1 - Network is down
The entire disaster takes seconds. The switch with the higher revision number wins, regardless of which one is "correct".
Configuring VTPv3 Safely
The solution is to use VTPv3 with a primary/secondary model:
Step 1: Set VTP Version to 3 on All Switches
CORE-SW1(config)# vtp version 3
DIST-SW1(config)# vtp version 3
DIST-SW2(config)# vtp version 3
ACC-SW1(config)# vtp version 3
ACC-SW2(config)# vtp version 3
ACC-SW3(config)# vtp version 3
Catalyst 9000 series ships with VTPv3 by default, but other platforms may require this command.
Step 2: Configure VTP Domain on All Switches
CORE-SW1(config)# vtp domain PRODUCTION
DIST-SW1(config)# vtp domain PRODUCTION
DIST-SW2(config)# vtp domain PRODUCTION
ACC-SW1(config)# vtp domain PRODUCTION
ACC-SW2(config)# vtp domain PRODUCTION
ACC-SW3(config)# vtp domain PRODUCTION
Step 3: Set Password on All Switches
In VTPv3, the password is hidden and used for authentication:
CORE-SW1(config)# vtp password productionvlans
Cryptographic key generated for VTP password
DIST-SW1(config)# vtp password productionvlans
Cryptographic key generated for VTP password
DIST-SW2(config)# vtp password productionvlans
Cryptographic key generated for VTP password
ACC-SW1(config)# vtp password productionvlans
Cryptographic key generated for VTP password
ACC-SW2(config)# vtp password productionvlans
Cryptographic key generated for VTP password
ACC-SW3(config)# vtp password productionvlans
Cryptographic key generated for VTP password
The "Cryptographic key generated" message means the password is hashed with SHA-1, not stored plaintext.
Step 4: Designate CORE-SW1 as Primary Server
CORE-SW1(config)# vtp mode server
CORE-SW1(config)# end
CORE-SW1# vtp primary vlan
This switch is becoming the VTP primary server for the PRODUCTION domain.
This two-step process ensures you consciously choose the primary. The vtp primary command requires you to be in EXEC mode (not config mode), adding a safety confirmation step.
Verify CORE-SW1 is primary:
CORE-SW1# show vtp status
VTP Version capable : 1 to 3
VTP version running : 3
VTP Domain Name : PRODUCTION
VTP Pruning Mode : Disabled
VTP Traps Generation : Enabled
Device ID : aabb.cc00.0100
Configuration last modified by : 192.168.1.1 at 10-20-2025 14:32:15 +00:00
Local updater ID : 10.0.0.1 (last local update)
Feature VLAN:
VTP Operating Mode : Server
Configuration Revision Number : 1
Maximum VLANs supported locally : 4094
Number of existing VLANs : 7
Configuration last modified by : 192.168.1.1 at 10-20-2025 14:32:15 +00:00
Primary Server : Yes
Key line: Primary Server: Yes
Step 5: Configure Distribution and Access Switches as Clients
DIST-SW1(config)# vtp mode client
DIST-SW2(config)# vtp mode client
ACC-SW1(config)# vtp mode client
ACC-SW2(config)# vtp mode client
ACC-SW3(config)# vtp mode client
Verify a client is synchronized:
DIST-SW1# show vtp status
VTP Version capable : 1 to 3
VTP version running : 3
VTP Domain Name : PRODUCTION
VTP Pruning Mode : Disabled
VTP Traps Generation : Enabled
Device ID : aabb.cc00.0200
Configuration last modified by : 192.168.1.1 at 10-20-2025 14:32:15 +00:00
Feature VLAN:
VTP Operating Mode : Client
Configuration Revision Number : 1
Maximum VLANs supported locally : 4094
Number of existing VLANs : 7
Observe: - VTP Operating Mode: Client (not server) - Configuration Revision Number: 1 (matches primary) - Number of existing VLANs: 7 (inherited from primary)
The client now has the same VLAN database as the primary server, received via VTP.
VTP Pruning
By default, VTP floods all VLANs across all trunk ports, wasting bandwidth when trunks carry VLANs not needed on both sides.
Example: Port Gi1/0/1 between CORE-SW1 and DIST-SW1 carries all 50 VLANs even though DIST-SW1 only has 3 access ports in VLANs 10, 20, and 30.
VTP Pruning allows switches to prune (remove) VLANs from trunk forwarding when no local ports belong to that VLAN.
Enable pruning on the primary server:
CORE-SW1(config)# vtp pruning
Verify:
CORE-SW1# show vtp status | include "Pruning"
VTP Pruning Mode : Enabled
Pruned VLANs don't propagate down a trunk if the downstream switch has no ports in that VLAN. This reduces flooding and improves performance on large networks.
Complete Lab Configuration
CORE-SW1 (Primary Server)
CORE-SW1(config)# vtp version 3
CORE-SW1(config)# vtp domain PRODUCTION
CORE-SW1(config)# vtp password productionvlans
CORE-SW1(config)# vtp pruning
CORE-SW1(config)# vtp mode server
CORE-SW1(config)# exit
CORE-SW1# vtp primary vlan
This device will become the VTP Primary Server for the PRODUCTION domain.
Do you want to continue? [yes/no]: yes
Create the VLANs on the primary server:
CORE-SW1(config)# vlan 10
CORE-SW1(config-vlan)# name Users
CORE-SW1(config-vlan)# exit
CORE-SW1(config)# vlan 20
CORE-SW1(config-vlan)# name Servers
CORE-SW1(config-vlan)# exit
CORE-SW1(config)# vlan 30
CORE-SW1(config-vlan)# name Management
CORE-SW1(config-vlan)# exit
CORE-SW1(config)# vlan 40
CORE-SW1(config-vlan)# name Voice
CORE-SW1(config-vlan)# exit
CORE-SW1(config)# vlan 50
CORE-SW1(config-vlan)# name Guest
CORE-SW1(config-vlan)# exit
CORE-SW1(config)# vlan 99
CORE-SW1(config-vlan)# name Native
CORE-SW1(config-vlan)# exit
CORE-SW1(config)# end
Verify VLANs were created and revision incremented:
CORE-SW1# show vlan brief
VLAN Name Status Ports
---- -------------------------------- --------- ----------------------------
1 default active
10 Users active
20 Servers active
30 Management active
40 Voice active
50 Guest active
99 Native active
CORE-SW1# show vtp status | include "Revision"
Configuration Revision Number : 6
Revision is now 6 (one increment per VLAN create).
DIST-SW1 and DIST-SW2 (Clients)
DIST-SW1(config)# vtp version 3
DIST-SW1(config)# vtp domain PRODUCTION
DIST-SW1(config)# vtp password productionvlans
DIST-SW1(config)# vtp mode client
DIST-SW1(config)# end
Wait 10-15 seconds for VTP updates to arrive. Verify:
DIST-SW1# show vtp status | include "Revision"
Configuration Revision Number : 6
DIST-SW1# show vlan brief | include "Users\|Servers\|Management"
10 Users active
20 Servers active
30 Management active
DIST-SW1 automatically received all VLANs from CORE-SW1.
Access Switches (Clients)
ACC-SW1(config)# vtp version 3
ACC-SW1(config)# vtp domain PRODUCTION
ACC-SW1(config)# vtp password productionvlans
ACC-SW1(config)# vtp mode client
ACC-SW1(config)# end
ACC-SW2(config)# vtp version 3
ACC-SW2(config)# vtp domain PRODUCTION
ACC-SW2(config)# vtp password productionvlans
ACC-SW2(config)# vtp mode client
ACC-SW2(config)# end
ACC-SW3(config)# vtp version 3
ACC-SW3(config)# vtp domain PRODUCTION
ACC-SW3(config)# vtp password productionvlans
ACC-SW3(config)# vtp mode client
ACC-SW3(config)# end
Verify all clients have synchronized revision:
ACC-SW1# show vtp status | include "Revision\|VTP Operating"
VTP Operating Mode : Client
Configuration Revision Number : 6
VTP Verification Commands
View detailed VTP status on primary:
CORE-SW1# show vtp status
VTP Version capable : 1 to 3
VTP version running : 3
VTP Domain Name : PRODUCTION
VTP Pruning Mode : Enabled
VTP Traps Generation : Enabled
Device ID : aabb.cc00.0100
Configuration last modified by : 192.168.1.1 at 10-20-2025 14:32:15 +00:00
Local updater ID : 10.0.0.1 (last local update)
Feature VLAN:
VTP Operating Mode : Server
Configuration Revision Number : 6
Maximum VLANs supported locally : 4094
Number of existing VLANs : 7
Configuration last modified by : 192.168.1.1 at 10-20-2025 14:32:15 +00:00
Primary Server : Yes
View VTP counters (summarized statistics):
CORE-SW1# show vtp counters
VTP Statistics
Summary Adverts received : 0
Subset Adverts received : 0
Request Adverts received : 0
Summary Adverts transmitted : 159
Subset Adverts transmitted : 0
Requests transmitted : 0
Number of config errors : 0
Number of digest errors : 0
High config or digest errors indicate: - Config errors: VLAN config mismatch between servers - Digest errors: VTP password mismatch (likely misconfiguration)
View VTP database on a client:
DIST-SW1# show vtp status
...
Feature VLAN:
VTP Operating Mode : Client
Configuration Revision Number : 6
Maximum VLANs supported locally : 4094
Number of existing VLANs : 7
Configuration last modified by : 192.168.1.1 at 10-20-2025 14:32:15 +00:00
The client shows the same revision number as the primary, confirming synchronization.
Troubleshooting VTP Issues
Symptom 1: Client Not Receiving VLANs from Server
Symptom: You create VLAN 25 on CORE-SW1 (primary server) but DIST-SW1 (client) doesn't receive it after 30 seconds.
Cause (Priority 1): Password mismatch between server and client.
Verification:
DIST-SW1# show vtp status | include "Digest\|Password"
If there's a mismatch, authentication fails and VTP updates are rejected.
Fix:
DIST-SW1(config)# vtp password productionvlans
Wait 10 seconds, then:
DIST-SW1# show vlan brief | include "25"
25 Research active
VLAN 25 now appears.
Cause (Priority 2): Domain name mismatch.
Verification:
DIST-SW1# show vtp status | include "Domain Name"
VTP Domain Name : LAB
If the domain is "LAB" but primary is in "PRODUCTION", no synchronization occurs.
Fix:
DIST-SW1(config)# vtp domain PRODUCTION
Cause (Priority 3): DIST-SW1 is in server mode instead of client mode.
Verification:
DIST-SW1# show vtp status | include "VTP Operating Mode"
VTP Operating Mode : Server
Two servers in the same domain don't auto-sync; they only update if manually created.
Fix:
DIST-SW1(config)# vtp mode client
Wait 10 seconds:
DIST-SW1# show vlan brief
VLAN Name Status Ports
---- -------------------------------- --------- ----------------------------
10 Users active
20 Servers active
25 Research active
Symptom 2: Revision Number Suddenly Increases Without Manual VLAN Changes
Symptom: You check CORE-SW1 and the revision jumps from 6 to 47 without anyone creating VLANs.
Cause: A switch with a higher revision number was connected to the trunk and caused the network to synchronize to its (outdated) database.
Verification:
CORE-SW1# show vtp status | include "Revision"
Configuration Revision Number : 47
CORE-SW1# show vlan brief
VLAN Name Status Ports
---- -------------------------------- --------- ----------------------------
1 default active
10 Users active
Check the updater ID:
CORE-SW1# show vtp status | include "Local updater\|Configuration last modified"
Local updater ID : 10.0.0.200 (last local update)
Configuration last modified by : 192.168.1.2 at 10-20-2025 15:47:22 +00:00
The Local updater ID is 10.0.0.200 (DIST-SW1's IP), not 10.0.0.1 (CORE-SW1). This means DIST-SW1 pushed an update to the primary.
Cause: DIST-SW1 was accidentally configured as server instead of client, or it was imported from another domain with a higher revision.
Fix:
DIST-SW1(config)# vtp mode client
Now DIST-SW1 receives from the primary; it doesn't push updates.
Prevention: Always use VTPv3 with a designated primary server. Secondary servers (clients) cannot increment the revision.
Symptom 3: VTP Password Error
Symptom: Syslogs show "VTP: Mismatched password in advertisement from {device-id}".
Cause: One switch has a different VTP password than others.
Verification:
CORE-SW1# show vtp status | include "Domain\|Version"
VTP Domain Name : PRODUCTION
VTP version running : 3
DIST-SW1# show vtp status | include "Domain\|Version"
VTP Domain Name : PRODUCTION
VTP version running : 3
Domains and versions match, but password is different. VTPv3 uses a hidden password, so you can't directly view it. Instead, check authentication:
CORE-SW1# show vtp counters | include "digest"
Number of digest errors : 12
High digest error count = authentication failure.
Fix: Set the same password on both switches:
DIST-SW1(config)# vtp password productionvlans
Verify digest errors clear:
CORE-SW1# show vtp counters | include "digest"
Number of digest errors : 0
Key Takeaways
- VTP revision numbers are a VLAN killswitch: A switch with a higher revision number overwrites the entire VLAN database on all other switches, regardless of which one is "correct."
- Use VTPv3 with a primary server: The primary/secondary model prevents secondary servers from incrementing the revision, eliminating revision collision disasters.
- Always set a domain and password: Without a domain name, VTP doesn't activate. Without a password, any switch can participate. Both are required for safe VTP.
- Transparent mode is safer than client mode for test switches: If you want a switch to have its own VLAN database without participating in synchronization, use transparent mode instead of client mode (clients are read-only; transparent switches can have local VLANs).
- Many networks disable VTP entirely: In modern deployments, VTP is often set to "off" mode and VLANs are manually configured on each switch or provisioned via automation. This eliminates the revision number risk entirely.