Master native VLAN configuration on Cisco Catalyst switches, understand VLAN hopping attacks, and implement security best practices to protect your switched network.
The native VLAN is one of the most overlooked and misunderstood aspects of VLAN trunking. Leaving it at the default (VLAN 1) introduces a serious security vulnerability and creates operational complications. Understanding native VLAN configuration, detection of mismatches, and protection against VLAN hopping attacks is essential for secure network design.
What is the Native VLAN?
The native VLAN is the VLAN assigned to untagged frames on a trunk link. When a switch receives an untagged frame on a trunk port, it automatically assigns the frame to the native VLAN. Similarly, when a switch transmits a frame belonging to the native VLAN on a trunk port, it sends the frame untagged (without the 802.1Q tag).
Why Untagged Frames Exist
This behavior originates from 802.1Q's historical design. When 802.1Q was new, many older network devices didn't support 802.1Q tagging. By sending the native VLAN untagged, those legacy devices could still communicate on the shared trunk link without understanding tags. Modern networks no longer need this compatibility, but the behavior persists for backward compatibility.
Native VLAN and Management Traffic
Historically, the native VLAN was used for management traffic on switches:
VLAN 1 (native) on trunk:
- Management IP address (192.168.1.1)
- SNMP community strings
- SSH/Telnet access
- Spanning Tree Protocol frames
- Other management protocols
In this design, management frames sent untagged on a trunk would reach the switch management interface, allowing remote management via the trunk link. This became the default behavior because VLAN 1 was automatically the native VLAN on all trunks.
The Security Problem with VLAN 1
Leaving VLAN 1 as the native VLAN on production trunks is a security vulnerability because:
- Default connectivity: VLAN 1 exists on all switches by default, so any switch automatically has a management interface in VLAN 1
- Untagged traffic: Any untagged frame on a trunk reaches VLAN 1 and potentially the management interface
- Attack vector: An attacker who gains access to any switch port (even a compromised access port) could send untagged frames to the trunk, and those frames would reach VLAN 1 and the management interface
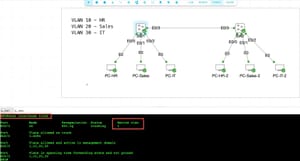
VLAN Hopping Attack Scenario
Consider an access switch with an attacker-controlled machine on an access port:
Topology:
Attacker PC on ACC-SW1 Gi1/0/1 (VLAN 10)
ACC-SW1 Gi1/0/23 trunk → DIST-SW1
DIST-SW1 management IP in VLAN 1
Attack steps:
1. Attacker crafts a frame destined for DIST-SW1 management IP
2. Attacker sends this frame as untagged (no 802.1Q tag)
3. ACC-SW1 receives the untagged frame on the access port
4. ACC-SW1 normally tags this as VLAN 10 (the access port's VLAN)
5. However, with a double-tagging attack (see below), the attacker can bypass this
6. Frame reaches DIST-SW1 VLAN 1 untagged
7. Frame reaches DIST-SW1 management interface
8. Attacker gains access to switch management
This attack is called VLAN hopping and leverages the native VLAN vulnerability. By changing the native VLAN to an unused VLAN (like VLAN 99), you eliminate this attack vector.
Changing the Native VLAN
Change the native VLAN from VLAN 1 to an unused VLAN on all trunk ports:
ACC-SW1# configure terminal
ACC-SW1(config)# interface GigabitEthernet 1/0/23
ACC-SW1(config-if)# switchport trunk native vlan 99
ACC-SW1(config-if)# end
DIST-SW1# configure terminal
DIST-SW1(config)# interface GigabitEthernet 1/0/24
DIST-SW1(config-if)# switchport trunk native vlan 99
DIST-SW1(config-if)# end
After changing the native VLAN, both sides of the trunk must use the same native VLAN or communication fails.
Verification After Native VLAN Change
Verify the native VLAN on each trunk:
ACC-SW1# show interfaces GigabitEthernet 1/0/23 trunk
Port Mode Encapsulation Status Native vlan
Gi1/0/23 on 802.1q trunking 99
DIST-SW1# show interfaces GigabitEthernet 1/0/24 trunk
Port Mode Encapsulation Status Native vlan
Gi1/0/24 on 802.1q trunking 99
Both sides now use VLAN 99 as the native VLAN. Untagged frames on these trunks belong to VLAN 99, not VLAN 1.
Detecting Native VLAN Mismatches
If the native VLAN differs between the two ends of a trunk, Cisco Discovery Protocol (CDP) detects the mismatch and issues a warning. This is a critical detection mechanism for catching configuration errors:
! Incorrect configuration: DIST-SW1 still has native VLAN 1
DIST-SW1(config-if)# switchport trunk native vlan 1
! ACC-SW1 detects the mismatch
ACC-SW1# show interfaces GigabitEthernet 1/0/23 trunk
%Native VLAN mismatch detected on Port Gi1/0/23 (Native VLAN 99),
with Port DIST-SW1 Gi1/0/24 (Native VLAN 1).
Port Mode Encapsulation Status Native vlan
Gi1/0/23 on 802.1q trunking 99
Port Vlans allowed on trunk
Gi1/0/23 10,20,30,40,50,99
Port Vlans allowed and active in management domain
Gi1/0/23 10,20,30,40,50,99
Port Vlans in spanning-tree forwarding state and not pruned
Gi1/0/23 10,20,30,40,50,99
Even though CDP warns of the mismatch, the trunk still forwards traffic. Untagged frames sent by ACC-SW1 (VLAN 99) arrive at DIST-SW1 on the untagged trunk and are assigned to DIST-SW1's native VLAN (1). This causes traffic destined for VLAN 99 to arrive in VLAN 1, breaking communication.
Always fix native VLAN mismatches immediately. The warning indicates a serious configuration error.
VLAN 1 Never Fully Disappears
VLAN 1 is special on all Cisco switches. You cannot fully delete it, and it will recreate itself after a reload:
ACC-SW1# configure terminal
ACC-SW1(config)# no vlan 1
ACC-SW1(config)# end
ACC-SW1# write memory
ACC-SW1# show vlan brief | include "^1"
1 default active
! After reload, VLAN 1 is recreated
ACC-SW1# reload
! VLAN 1 exists again
ACC-SW1# show vlan brief | include "^1"
1 default active
This is intentional. VLAN 1 serves as a fallback; if a switch cannot access its vlan.dat file on startup, VLAN 1 ensures basic connectivity. However, do not use VLAN 1 for user traffic or management. Leave it unused.
Security Best Practice: Move Management Out of VLAN 1
Beyond changing the native VLAN, move management traffic out of VLAN 1 entirely. Configure the switch management IP in an unused VLAN:
ACC-SW1# configure terminal
! Create the Management VLAN
ACC-SW1(config)# vlan 30
ACC-SW1(config-vlan)# name Mgmt
ACC-SW1(config-vlan)# exit
! Create a Switched Virtual Interface (SVI) for management
ACC-SW1(config)# interface Vlan 30
ACC-SW1(config-if)# ip address 10.10.30.11 255.255.255.0
ACC-SW1(config-if)# description Management-Interface
ACC-SW1(config-if)# no shutdown
ACC-SW1(config-if)# exit
! Assign one access port to VLAN 30 for out-of-band management
ACC-SW1(config)# interface GigabitEthernet 1/0/15
ACC-SW1(config-if)# switchport mode access
ACC-SW1(config-if)# switchport access vlan 30
ACC-SW1(config-if)# description Management-Access
ACC-SW1(config-if)# no shutdown
ACC-SW1(config-if)# exit
ACC-SW1(config)# end
ACC-SW1# write memory
Now management is isolated in VLAN 30, not in the vulnerable VLAN 1. Management connections via trunk links still reach VLAN 1 (if native VLAN is changed to 99, untagged frames go there), but the actual management interface is in VLAN 30.
Blocking Management VLAN from Trunks
For additional security, remove the management VLAN from the allowed VLAN list on user-facing trunks. This prevents users from seeing or accessing management traffic:
ACC-SW1# configure terminal
ACC-SW1(config)# interface GigabitEthernet 1/0/23
ACC-SW1(config-if)# switchport trunk allowed vlan 10,20,40,50,99
! Note: VLAN 30 (Management) is not in this list
ACC-SW1(config-if)# end
Management traffic stays on the switch; only user VLANs cross to the distribution switch.
VLAN Tagging on the Native VLAN: Advanced Configuration
In some edge cases, you might want the switch to tag frames even in the native VLAN. This is rare but useful for troubleshooting or special configurations. The vlan dot1q tag native command enables this:
ACC-SW1# configure terminal
ACC-SW1(config)# vlan dot1q tag native
ACC-SW1(config)# end
! Now even native VLAN frames are tagged on trunks
ACC-SW1# show interfaces trunk
Port Mode Encapsulation Status Native vlan
Gi1/0/23 on 802.1q trunking 99
After executing this command, the native VLAN frames on trunks will be tagged with a 802.1Q header. This breaks compatibility with devices expecting untagged native VLAN frames, so use it only if you understand the consequences.
Complete Native VLAN Configuration Example
Here's a complete configuration for native VLAN security across the lab topology:
! Configure all switches with VLAN 99 as native on all trunks
CORE-SW1# configure terminal
! Gi1/0/2 trunk to DIST-SW1
CORE-SW1(config)# interface GigabitEthernet 1/0/2
CORE-SW1(config-if)# switchport mode trunk
CORE-SW1(config-if)# switchport trunk native vlan 99
CORE-SW1(config-if)# switchport trunk allowed vlan 10,20,30,40,50,99
CORE-SW1(config-if)# switchport nonegotiate
CORE-SW1(config-if)# exit
! Gi1/0/3 trunk to DIST-SW2
CORE-SW1(config)# interface GigabitEthernet 1/0/3
CORE-SW1(config-if)# switchport mode trunk
CORE-SW1(config-if)# switchport trunk native vlan 99
CORE-SW1(config-if)# switchport trunk allowed vlan 10,20,30,40,50,99
CORE-SW1(config-if)# switchport nonegotiate
CORE-SW1(config-if)# exit
CORE-SW1(config)# end
CORE-SW1# write memory
! Configure on DIST-SW1 and DIST-SW2 similarly
! Configure on ACC-SW1, ACC-SW2, ACC-SW3 similarly
Verification and Troubleshooting
Symptom: Native VLAN mismatch warning appears
Cause: The two ends of a trunk have different native VLANs.
Fix: Ensure both sides match. Find the mismatch:
ACC-SW1# show interfaces GigabitEthernet 1/0/23 trunk | include Native
Native vlan
Native vlan 99
! Check the remote switch via SSH or CDP
DIST-SW1# show interfaces GigabitEthernet 1/0/24 trunk | include Native
Native vlan
Native vlan 1
! The mismatch is clear. Fix DIST-SW1
DIST-SW1(config)# interface GigabitEthernet 1/0/24
DIST-SW1(config-if)# switchport trunk native vlan 99
DIST-SW1(config-if)# end
! Verify the mismatch is gone
ACC-SW1# show interfaces GigabitEthernet 1/0/23 trunk | include mismatch
! No output means no mismatch
Symptom: Management access lost after changing native VLAN
Cause: You changed the native VLAN but didn't move the management IP to a proper management VLAN, so management traffic is now in an isolated VLAN.
Fix: Configure a management VLAN and move the management IP:
DIST-SW1# configure terminal
DIST-SW1(config)# vlan 30
DIST-SW1(config-vlan)# name Mgmt
DIST-SW1(config-vlan)# exit
DIST-SW1(config)# interface Vlan 30
DIST-SW1(config-if)# ip address 10.10.30.2 255.255.255.0
DIST-SW1(config-if)# no shutdown
DIST-SW1(config-if)# exit
DIST-SW1(config)# end
DIST-SW1# write memory
! Verify management interface
DIST-SW1# show interface Vlan 30
Vlan30 is up, line protocol is up
Hardware is Ethernet SVI, address is aabb.cc00.0202 (bia aabb.cc00.0202)
Internet address is 10.10.30.2/24
Symptom: Untagged frames reaching the wrong VLAN on the far end of a trunk
Cause: Native VLAN mismatch. Untagged frames sent by one switch arrive at the other in the wrong VLAN.
Fix: Ensure native VLANs match on both sides of the trunk:
! Verify both sides
ACC-SW1# show interfaces trunk | grep Native
Native vlan
Native vlan 99
DIST-SW1# show interfaces trunk | grep Native
Native vlan
Native vlan 99
! If they match and the problem persists, check VLAN routing
! The VLANs might not have connectivity between switches
ACC-SW1# show vlan brief | grep 99
99 Native active
Symptom: Can't manage switch via trunk after changing native VLAN
Cause: Management traffic is not properly configured or routed after the native VLAN change.
Fix: Ensure management VLAN has connectivity and proper routing:
! Verify management interface exists
DIST-SW1# show interface Vlan 30
Vlan30 is up, line protocol is up
Internet address is 10.10.30.2/24
! Verify VLAN 30 exists and is active
DIST-SW1# show vlan id 30
VLAN Name Status Ports
---- -------------------------------- --------- ------
30 Mgmt active
! Verify a port is assigned to VLAN 30
DIST-SW1# show vlan id 30 | include Gi
! If no ports show, assign one
DIST-SW1(config)# interface GigabitEthernet 1/0/15
DIST-SW1(config-if)# switchport mode access
DIST-SW1(config-if)# switchport access vlan 30
DIST-SW1(config-if)# no shutdown
DIST-SW1(config-if)# end
Key Takeaways
- Change the native VLAN from VLAN 1 to an unused VLAN (like VLAN 99) on all trunks to prevent VLAN hopping attacks
- Native VLAN mismatch is detected by CDP and prevents proper communication across trunks; always ensure both ends match
- Move management traffic into a dedicated management VLAN (VLAN 30) out of the vulnerable VLAN 1, and assign an out-of-band management port
- VLAN 1 cannot be fully deleted and will recreate itself after reload; avoid using it for any traffic
- Verify native VLAN configuration with
show interfaces <port> trunkand immediately fix any mismatches detected by CDP - Use
vlan dot1q tag nativeonly in rare edge cases where native VLAN tagging is required for specific network scenarios